According to Matt Ahlgre (2022, WSR), the ransomware or 'data hijacking' attacks occur every 10 seconds and it is estimated that the global cost of cyber-threats in 2025 will be 10.5 trillion.
However, in spite of these data, the future of the cybersecurity looks promising. Numerous advances in detection and response to these threats, using technologies such as machine learning or deep learning, they are able to detect them at an early stage.
In 2020, Garner establishes "SECURITY MONITORING PYRAMID" o "triangle of virtuecovering most of the cyber security spectrum through threat detection, prevention and response solutions:
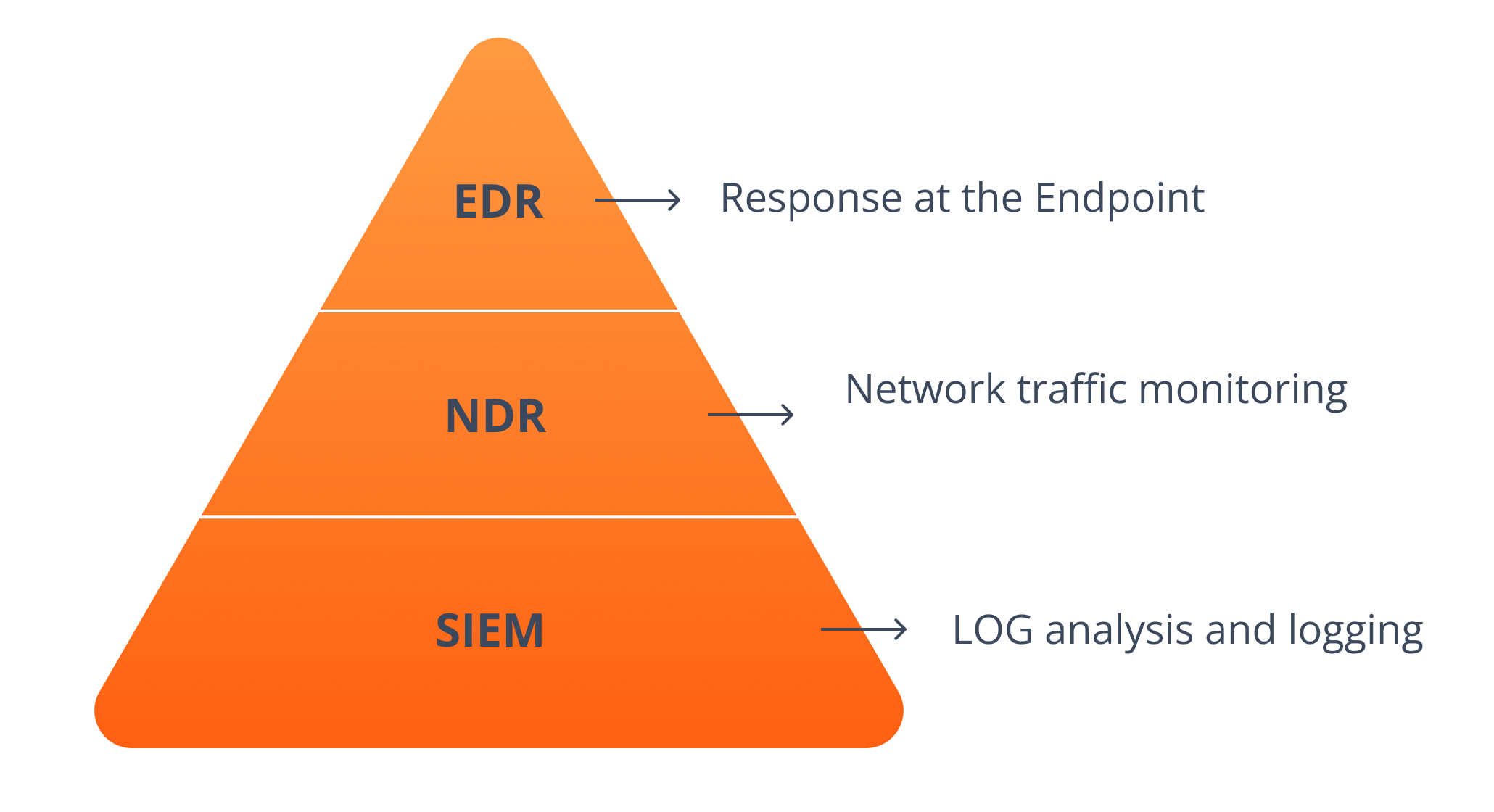
| EDR | EDR, Endpoint detection and response (EPR) is a system that monitors suspicious activity at endpoints (computers connected to a network, not the network itself). It enables the collection and analysis of data on endpoint security risks with the objective of detecting security breaches as they occur, providing a rapid response to identified or suspected threats. The capabilities and details of an EDR system can vary substantially depending on how it is implemented. |
| NDR | Network detection and response allows you to monitor traffic for threats and suspicious behaviour that could cause a security breach in the future. Traditional signature-based methods are no longer 100% effective against modern threats, creating a false illusion of security for many businesses. Greater and deeper network visibility provides businesses with an additional layer of security and advanced prevention capabilities. |
| SIEM | Security information and event management, is the umbrella term for the services of software that collect and examine (suspicious) behaviour in their digital infrastructure from numerous sources. SIEM's main function? Collect security information from databases, servers, domain controllers and network hardware. Identify risks, identify trends, examine alarms and locate network vulnerabilities by applying analytics to this data. |
Why use an NDR?
SIEM programmes can generate comprehensive reports on incidents and events, including malware and other transgressions. However, they are not able to adjust on their own and are often unable to it is difficult to interpret large amounts of data.
An advanced NDR, in contrast, it can quickly decrypt a large number of protocols to identify suspicious attacks and patterns of behaviour with sufficient context and evidence for analysts to act with confidence. In addition, NDR complements EDR by filling in the gaps that EDR does not detect.
Each of the SIEM, EDR and NDR has particular advantages and disadvantages. When all three are combined, each element can reinforce the others.
HOW TO STOP RANSOMWARE
Ransomware attacks are changing, in fact, new generations often use stolen credentials in order to gain privileged access.
The attacker's intent is to get administrator access to the domain controller, as from this position it is easy to gain access to most of the valuable data. It is also possible to deploy ransomware incredibly quickly, using administration tools that have GPOs (Group Policy Objects).
The modern RansomOps attacks do not deploy the binary code all the way to the endSo by the time you see the attack, it is too late. Early detection of it, in the earlier stages, is vital.
For this reason, it is absolutely essential monitor the use of all privileged accounts. We have observed that this is certainly one of the most valuable attack detection signals.
Recommendations:
Prevention:
- Assess the level of security on a regular basis and implement a plan to prioritise corrections according to the level of risk. Special attention should be paid to the most vulnerable services such as RDP, FTP and remote access infrastructure.
- Enable multi-factor authentication in remote access infrastructures or identity providers.
- Implement controls, prevention policies and rules to buy time to respond to the threat.
- Pay special attention to privileged accounts. The use of bridge servers and management systems for these accounts will make it more difficult for attackers.
Detection:
- From the time the ransomware operator gains access to the time it is deployed, there is a time lag. That's why we believe in investing in detection and response across the network, cloud, endpoint and identity infrastructure, maximising the chances of early detection.
Research and response:
- Monitor critical alerts on an ongoing basis. Reinforcing internal teams, through MDRs, managed detection and response systems, or with managed security service providers.
- Look for surges of activity in your DMZ prior to initial access along with open source OSINT intelligence. This can provide an early assessment of a cyber-attack.
The network detection and response platform driven by the Vectra AI monitors privileged account abuse, network traffic, and even from the cloud, data centre or IoT devices, looking for telltale signs of compromise and attacker behaviour indicative of a ransomware attack, such as:
- Recognition and lateral movement
- Command and control
- Initial access: Cyber attackers look for vulnerabilities in systems and services over the internet via RDP, FTP or VPN servers, as they allow initial access to companies and the cloud. In many cases, it takes hours, days or even weeks for the attack to be deployed, so it is during this time that constant vigilance is really required.
This level of analysis is impossible to perform manually, but it is simple for Vectra's AI-powered platform. Vectra integrates with existing security tools to take action on affected accounts and devices.
Exceltic expands its cybersecurity department with this new alliance que proporcionará a sus clientes soluciones de detección y respuesta de red.